The Illusion of Third Party Risk Management
Ashwini Rawal
Feb 25, 2026
•
7 Min
The Illusion of Oversight
What many call a third-party risk program is often a growing backlog of assessments, increasingly disconnected from measurable risk reduction or board-level assurance.
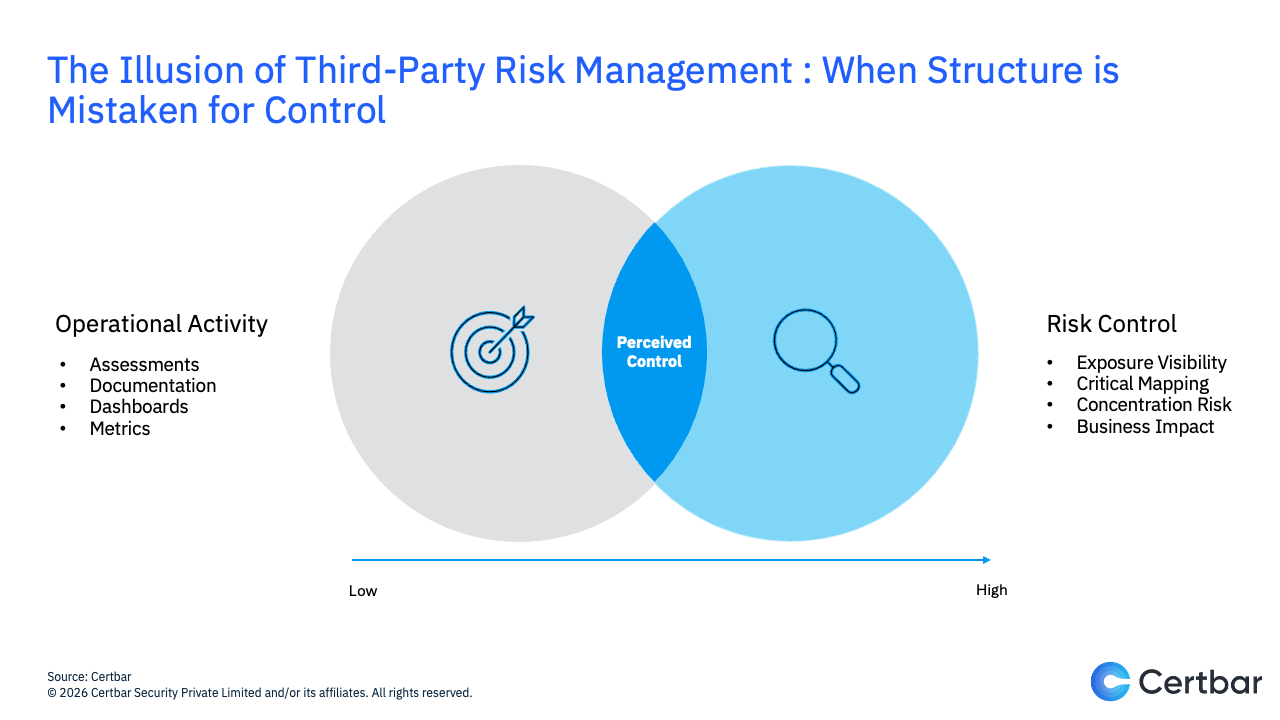
Many enterprises today speak with confidence about their third-party risk management programs. The documentation exists. Assessments are conducted. Dashboards are populated.
From a structural standpoint, governance appears present. Yet the presence of structure does not automatically imply the presence of control.
This is where the illusion begins.
An Expanding Web of Dependence
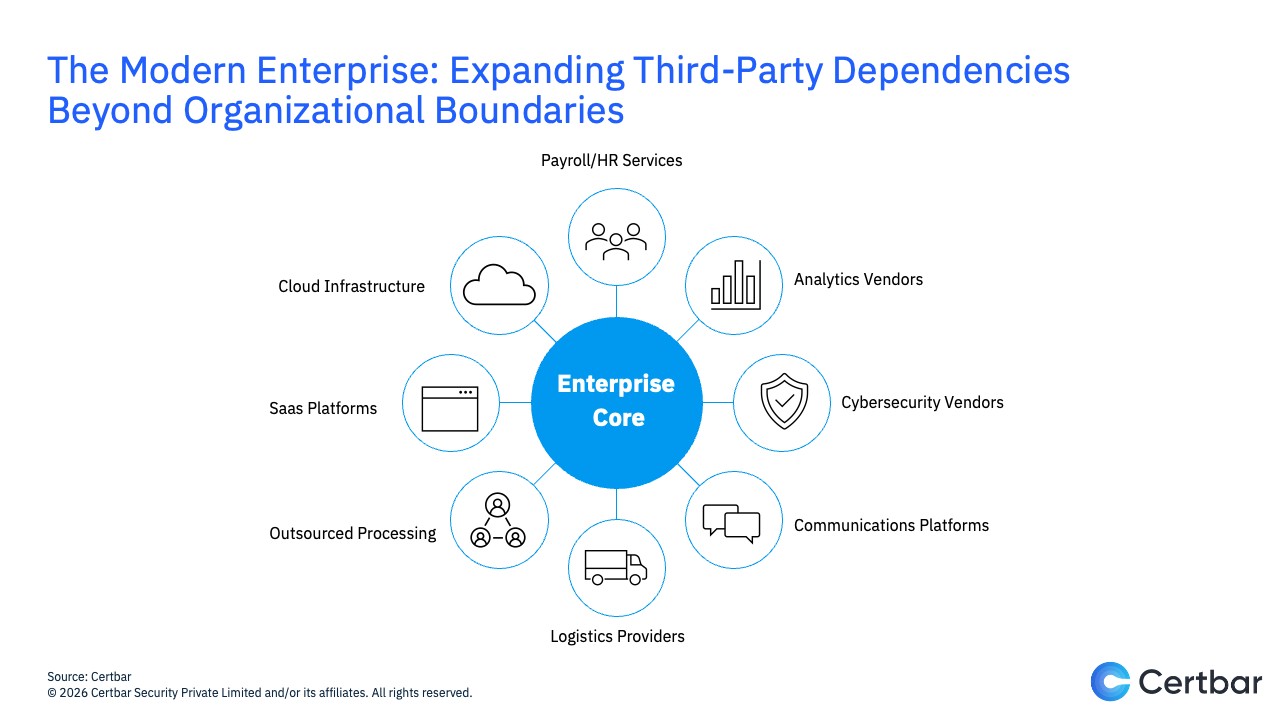
The modern enterprise no longer operates within clearly defined organizational boundaries. Core applications may reside on cloud infrastructure, customer data may be managed through SaaS platforms, transactions may be processed by outsourced partners, and physical distribution may depend on logistics providers operating far beyond the firm’s direct control. Even critical support functions from analytics and cybersecurity to payroll and communications are frequently delivered by specialized external vendors.
The organization, in effect, is partially distributed. With distribution comes dependency, and with dependency comes risk that does not sit neatly within corporate walls.
Recognizing this, enterprises established Third-Party Risk Management (TPRM) programs. The intent was sound: to introduce discipline, visibility, and oversight into vendor relationships that materially affect operations.
For a time, that structure provided comfort.
When Process Begins to Replace Judgment
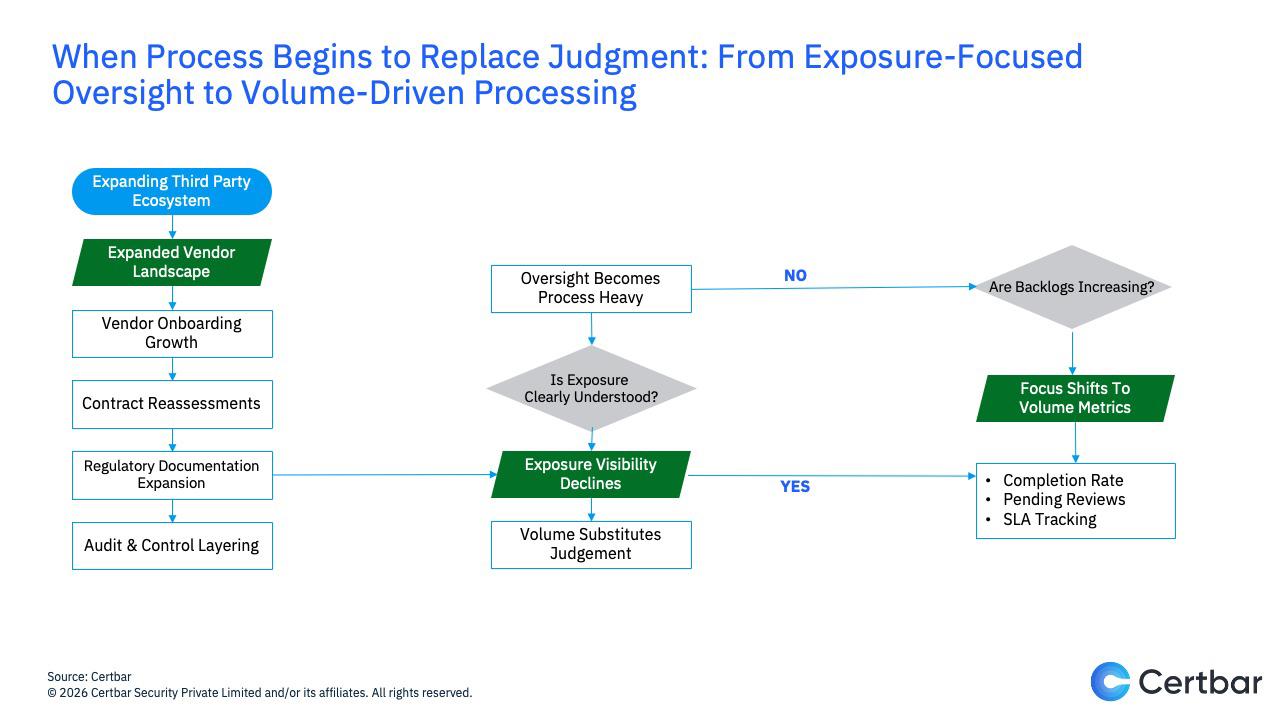
As third-party ecosystems expanded, oversight mechanisms expanded alongside them inevitably.
What began as a structured and manageable discipline gradually became more layered. Each new vendor required review, each contract renewal triggered reassessment, and evolving regulatory expectations translated into increasingly detailed documentation. Internal audits introduced additional layers of scrutiny, each designed to strengthen governance yet collectively adding operational complexity.
Each step, in isolation, was reasonable. Together, they subtly shifted the center of gravity. Over time, the third-party risk function found itself responding to volume rather than exposure. The discipline that began as a means of understanding risk increasingly became an exercise in processing it.
The question changed quietly. Instead of asking, “What risks do our third parties create?” teams began asking, “How many assessments remain outstanding?”
The distinction appears minor. It is not.
Backlogs accumulated gradually. Dashboards filled with status indicators. Completion rates were tracked with precision. Meetings that once centered on exposure began to focus on throughput and turnaround time. Concern for risk did not disappear; rather, what was easiest to measure began to take precedence over what was most important to understand.
Without deliberate intent, volume began to substitute for judgment.
Activity Without Assurance
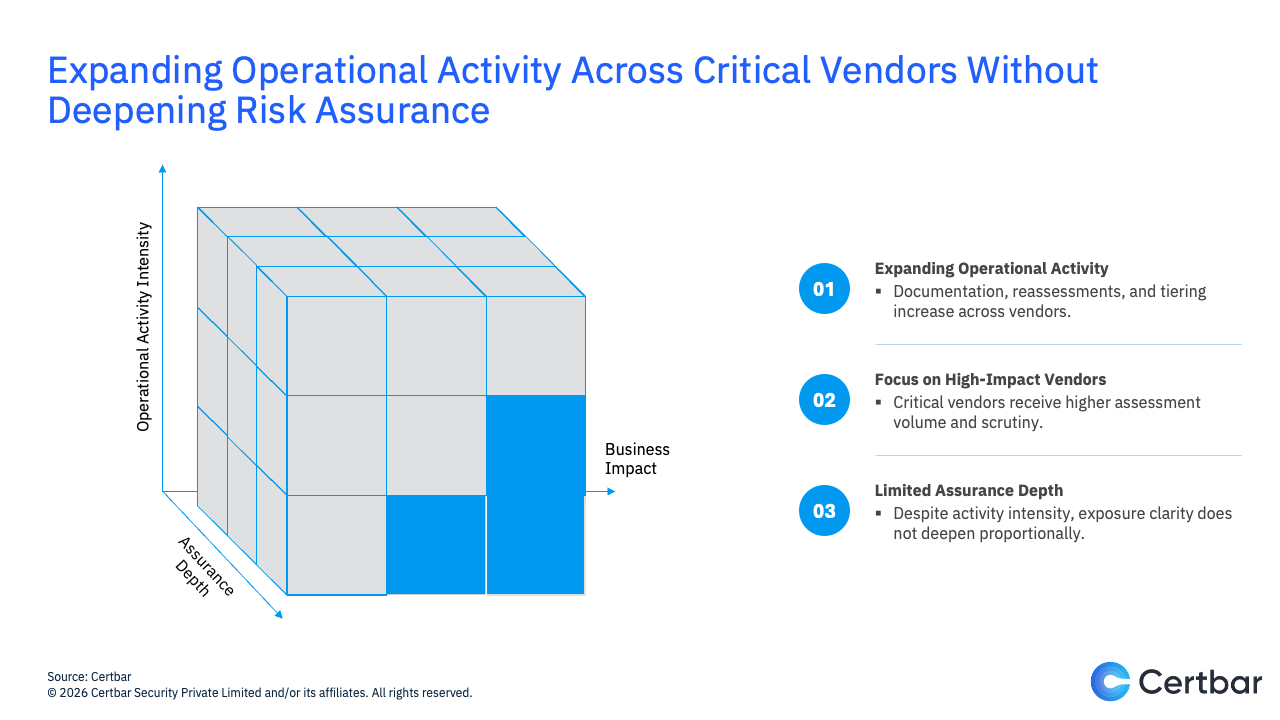
In many environments today, what is described as a third-party risk program operates in practice as an assessment engine. It generates documentation, tracks responses, categorizes vendors into predefined tiers, and records findings with procedural efficiency. From an operational standpoint, the system functions as designed.
And yet, when one steps back from the mechanics, a more fundamental question emerges:
Where is our material exposure truly concentrated?
Completing an assessment does not by itself reduce risk. A questionnaire answered, however comprehensive, does not automatically strengthen resilience. A vendor classified as “medium risk” does not, in isolation, clarify the operational consequences of failure. The act of reviewing is not the same as the act of understanding.
Without deliberate alignment to enterprise risk priorities, revenue dependency, data sensitivity, and operational criticality, third-party risk management can gradually assume an administrative character. It becomes defined by processing rather than by perspective. Structure remains intact, but assurance becomes uncertain.
What Should Thoughtful Leadership Ask?
When complexity increases, leadership must return to first principles.
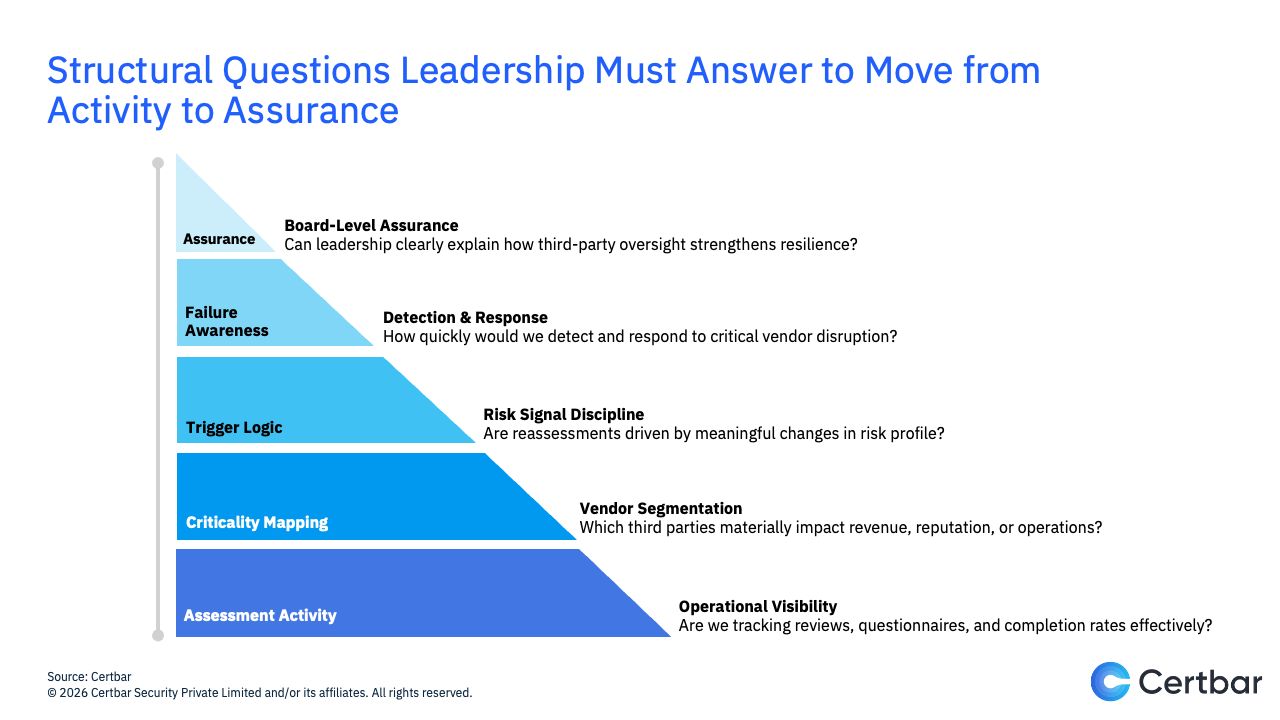
The relevant questions are not operational. They are structural.
- Which third parties, if disrupted, would materially affect our revenue or reputation?
- How quickly would we detect a failure in a critical vendor?
- Are reassessments triggered by meaningful changes in risk profile or by calendar cycles?
- Can we explain to the board how third-party oversight strengthens business resilience?
These questions are not accusatory. They are clarifying. They separate the existence of process from the presence of assurance.
Reframing Maturity
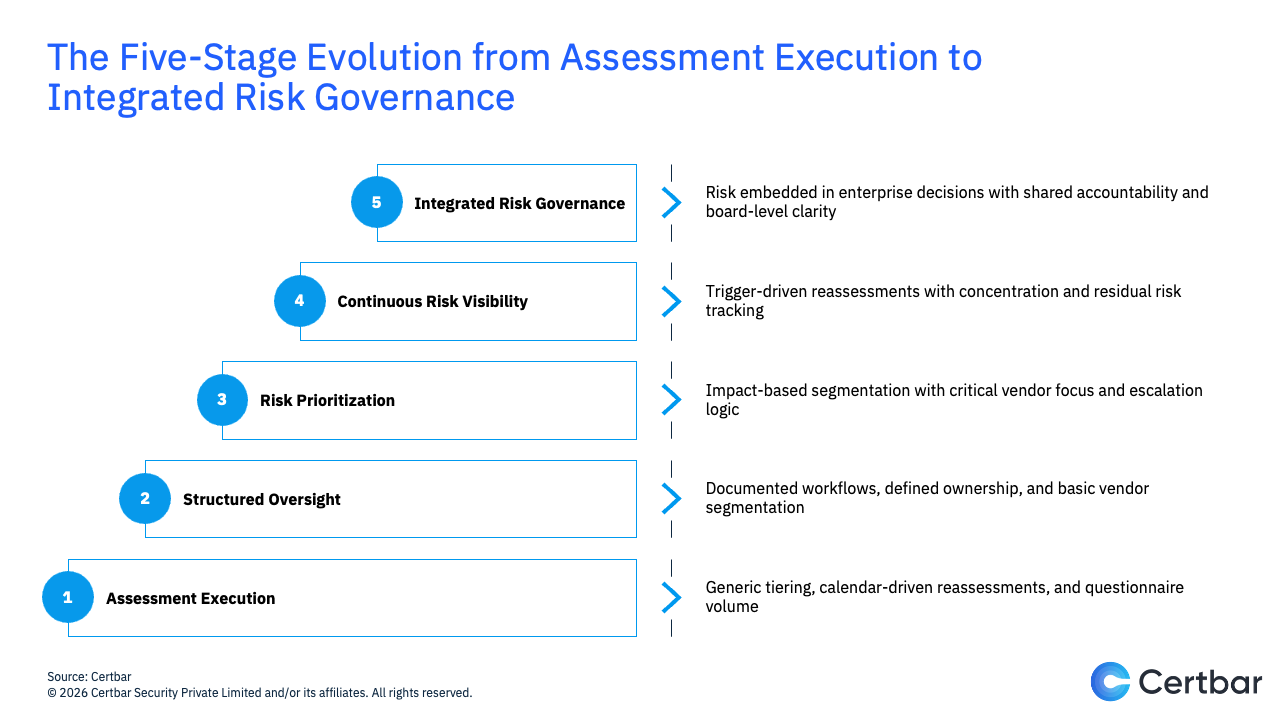
A mature third-party risk management program does not abandon assessments. It contextualizes them.
It begins with segmentation grounded in business impact rather than generic tiering. It prioritizes vendors whose failure would cascade across operations. It integrates risk data into enterprise decision-making instead of isolating it within procurement or security functions.
Continuous visibility replaces periodic surprise.
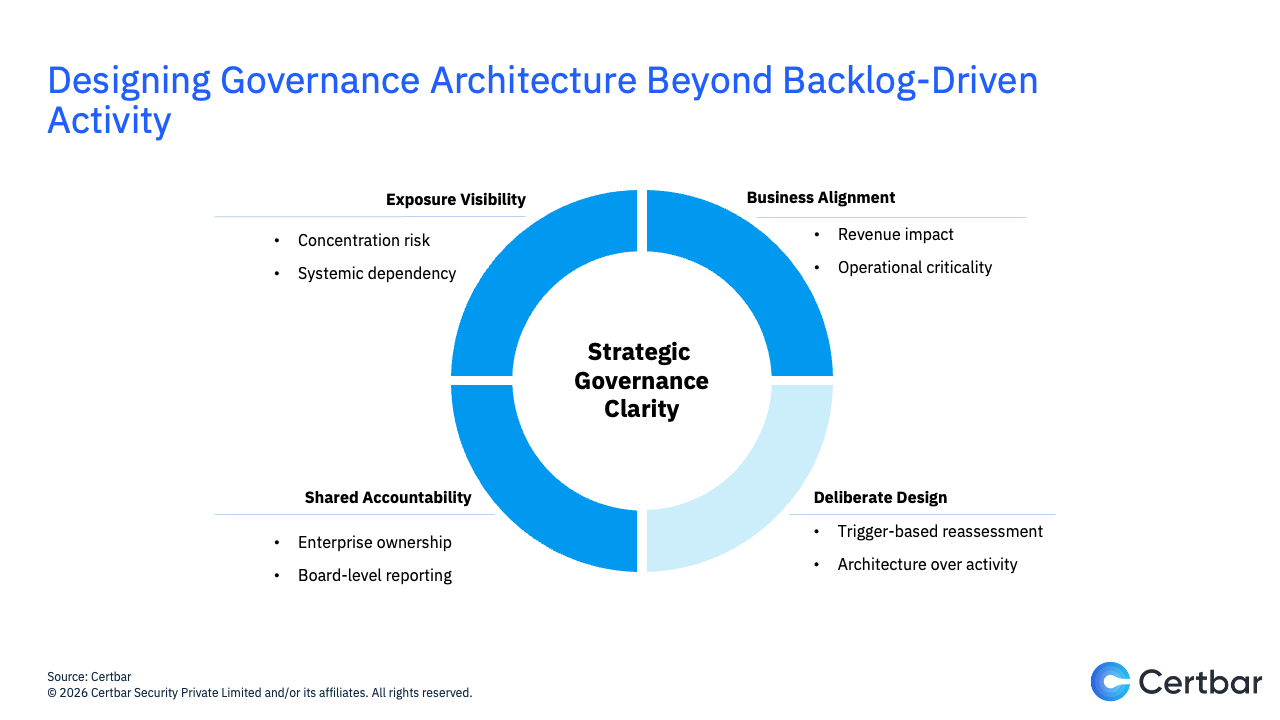
Reporting shifts from counting completed reviews to articulating concentration risk, systemic dependency, and residual exposure. Ownership expands. Third-party risk becomes a shared governance responsibility rather than a compliance function.
This is when assessment becomes an instrument rather than an endpoint.
Conclusion: The Strategic Distinction
There is nothing inherently problematic about a backlog. In growing organizations, backlogs often reflect demand, scale, and operational intensity. In that sense, a backlog is not a failure. It is a symptom of growth.
But it is not a strategy.
The difficulty arises when the accumulation of tasks begins to substitute for an understanding of exposure. When third-party risk management is experienced primarily as a queue to be processed rather than a risk landscape to be interpreted, motion can easily be mistaken for control.
Activity becomes reassuring because it is visible. Dashboards update. Metrics improve. Tickets close.
Assurance, however, is quieter. It requires deliberate design, an architecture that connects third-party oversight to enterprise risk, business continuity, and institutional resilience.
Backlogs generate activity.
Governance generates clarity.
And in the long run, it is clarity, not motion, that protects institutions.
Frequently Asked Questions (FAQs)
1. What is third-party risk management (TPRM)?
Third-Party Risk Management (TPRM) is the structured process by which organizations identify, assess, monitor, and govern risks arising from external vendors, service providers, and strategic partners. Its purpose is not merely to complete assessments, but to understand how third-party dependencies affect operational resilience, revenue stability, regulatory exposure, and institutional trust.
2. Why do many third-party risk programs become assessment-heavy?
As vendor ecosystems expand, oversight requirements expand with them. Regulatory expectations, internal audits, and contract renewals introduce additional review layers. Over time, the focus can shift from evaluating material exposure to managing assessment volume. What begins as exposure-focused governance can gradually evolve into process-driven administration.
3. Does completing vendor assessments reduce risk?
Not automatically. Completing a questionnaire documents risk posture, but documentation alone does not reduce exposure. Risk reduction occurs when assessment findings influence prioritization, remediation, monitoring, and executive decision-making. The act of reviewing is not the same as the act of mitigating.
4. What is the difference between activity and assurance in TPRM?
Activity refers to visible process metrics, completed assessments, closed tickets, SLA compliance, dashboard updates.
Assurance refers to clarity about material exposure which are concentration risk, systemic dependency, residual risk, and operational impact. Activity can be measured. Assurance must be designed.
5. How can leadership determine whether their TPRM program is mature?
A mature TPRM program:
- Segments vendors based on business impact rather than generic tiers
- Prioritizes critical dependencies over procedural uniformity
- Uses trigger-based reassessments instead of calendar-only cycles
- Integrates risk data into enterprise and board-level decision-making
- Reports exposure, not just throughput.
6. What questions should boards and executives ask about third-party risk?
Leadership should move beyond operational metrics and ask:
- Which vendors represent material revenue or operational dependency?
- How quickly would we detect a critical third-party failure?
- Where is our concentration risk most significant?
- Can we articulate how third-party oversight strengthens enterprise resilience?
7. What defines an integrated third-party risk governance model?
An integrated governance model embeds third-party risk into enterprise risk management, business continuity planning, and strategic decision frameworks. Ownership becomes shared across functions. Reporting reflects exposure concentration and systemic risk. Assessments become instruments of insight, not endpoints of compliance.
Share
Friday Briefing


